Research blog
-
Praktische ervaringen met automatische RAG-evaluatie
Kwaliteit is dé bottleneck om LLM-toepassingen in productie te brengen. In deze blogpost onderzoeken we in hoeverre de kwaliteit van RAG-toepassingen automatisch kan gemeten worden.
-
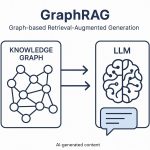
GraphRAG – Vers une génération augmentée par les graphes de connaissances
Les systèmes RAG (Retrieval-Augmented Generation) ont permis aux grands modèles de langage (LLM) de s’appuyer sur des données fiables. Mais ils restent limités, entre autres, dans leur capacité à contrôler les hallucinations. C’est là que GraphRAG entre en jeu : en combinant les LLM avec des graphes de connaissances, il améliore la précision, la transparence et la capacité de raisonnement des modèles.
-
HTTPS, Incognito, VPN, Tor… waartegen beschermt het ons?
Hoe kunnen we onszelf beschermen tegen de sporen die we achterlaten als we op het internet surfen? Er worden verschillende oplossingen voorgesteld, met hun voor- en nadelen.
-
Webinar: Crypto Agility – Prepare for the unexpected
Cryptography is essential in our society. Much of it is at risk of becoming insecure in the future due to powerful quantum computers. The current cryptography will have to be replaced by quantum-resistant alternatives. And even then, the crypto migrations will continue. Experience has taught us that such migrations are difficult, slow and expensive processes.
-
Ethiek en artificiële intelligentie: hoe een bias meten en corrigeren?
Dit artikel gaat in op de manier waarop algoritmische bias kan worden gemeten en op de verschillende manieren om deze te corrigeren om eerlijke voorspellingen te genereren.
-
HTTPS, Incognito, VPN, Tor… de quoi ça nous protège ?
Comment se protéger des traces que nous laissant en navigant sur Internet? Plusieurs solutions sont proposées, avec leurs avantages et inconvénients.
-
« Crypto Agility – Prepare for the unexpected » – Webinar by Smals Research (june 12, 2025)
Slides are available, recording will be soon…
-
Runner-up for Cybersecurity Innovation Europe Award
Smals Research is at the cradle of eHealth’s blind pseudonymization service. This innovation came in a very creditable second place this year at the prestigious Best Cybersecurity Innovation Europe awards, presented by Cybersec Europe in the presence of Prince Laurent. The jury praised the service for its innovative, practical and Belgian character, the simplicity of the solution and the potential…
-
Tech talk Cybersec Europe – Cryptographic agility in practice
Due to the threat of powerful quantum computers in the not so distant future, we need to replace our cryptography. We do this migration from old to new cryptography once, and then we are done, right? Not exactly. We have multiple cryptographic migrations behind us and, most likely, multiple in front of us. A more
-
Keynote Cybersec Europe: Resilience against quantum (and other) threats with crypto agility
Slides of keynote given at Cybersec Europe 2025. Public key cryptography is essential in our society. We use it constantly, for instance to secure digital communication. Powerful quantum computers could break this in the long term and are already a risk today. Someone who intercepts secure communication today may indeed be able to decipher it
Keywords:
analytics annexe_category Artificial intelligence big data blockchain BPM chatbot cloud computing cost cutting cryptography data center data quality development EDA egov Event GIS Knowledge Graph Machine Learning methodology Mobile Natural Language Processing NLP Open Source PaaS Privacy Productivity quantum computing Security software design